Python for Cybersecurity - by Howard E Poston (Paperback)
$22.35Save $7.65 (26% off)
In Stock

Eligible for registries and wish lists
About this item
Additional product information and recommendations
Frequently bought together
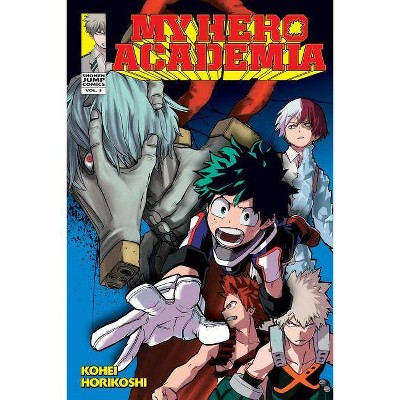
$6.71
MSRP $9.99
Save $5 when you spend $25 on select books
4.9 out of 5 stars with 60 ratings